Using the open RISC-V ISA is a great starting point for creating a domain-specific processor that combines application-specific capabilities and access to portable software. But how do you create an optimized ISA, profiling software and experimenting with adding/removing instructions, in a smart and easy way? In other words, how do you customize an existing RISC-V processor efficiently?
How to modify the instruction set?
The industry will generally offer you two approaches. Either you do it manually or you automate the process as much as possible.
The manual approach
The old-fashioned way to modify the instruction set would be to:
- Modify the instruction set simulator (ISS) to change the ISA.
- Update the SDK to reflect the new set of target instructions.
This requires an extensive amount of manual work with associated technical risks. The resulting SDK will almost certainly need to make any custom instructions available as intrinsics or as inline assembler code. The alternative of modifying and verifying the compiler is costly in effort, but the end result is much better for the software developers. Similarly, if a processor is extended, traditionally it would be necessary to modify the microarchitecture by editing the RTL and then verify it against the ISS as the golden reference.
The automated approach
In contrast, describing the ISA in a processor description language like CodAL significantly improves the efficiency of this process using design automation tools. Codasip Studio can automatically generate both the ISS and a new compiler for the modified ISA, making the processor customization process more straightforward. But the CodAL processor description language is not just limited to creating instruction-accurate descriptions – it can also be used to describe microarchitecture (cycle-accurate). The consistency of the two descriptions can be checked within the Studio environment using static analysis.
A far easier approach is to not just to start with the RISC-V ISA, but with a complete RISC-V processor core design described in CodAL.
Automating the customization of a RISC-V CPU with Codasip Studio
Codasip’s RISC-V processors are all designed in Codasip Studio using the CodAL language. The range of cores spans simple 32-bit embedded cores to 64-bit Linux-capable application processors with multi-core capabilities. Thus, you can choose a processor that meets known baseline requirements such as pipeline depth and/or OS support, and then focus on creating custom extensions to improve performance. Starting with an already-proven processor design means that the microarchitecture for any new instructions is incremental, saving time and significantly reducing risk.
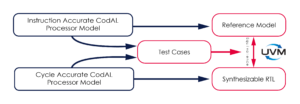
Codasip Studio can be used to generate the HDK including the RTL, a testbench, EDA scripts, and a UVM environment. The UVM environment enables the all-important verification of the new processor RTL against its golden ISS reference. The generated UVM environment includes default cover points and assertions for key areas of functionality such as register files, bus protocols, memories, and caches. The third-party RTL simulator can measure the functional and RTL code coverage achieved.
After extending the microarchitecture, Codasip Studio profiler provides coverage analysis tools to assess code coverage of the CodAL, including line, condition, and expression coverage. In order to achieve acceptable code coverage, Codasip Studio provides random assembler generators to exercise the code very thoroughly. In difficult corner cases, it may be necessary to write directed tests.
All-in-all a Codasip RISC-V processor licensed as CodAL source code can be efficiently modified in the Codasip Studio environment and thoroughly verified. This is a cost-effective and super-efficient approach to creating domain-specific processors.
Learn more in our white paper “Creating Domain-Specific Processors with RISC-V custom ISA instructions”.
